How We Help
Author Archives: ISG Tech
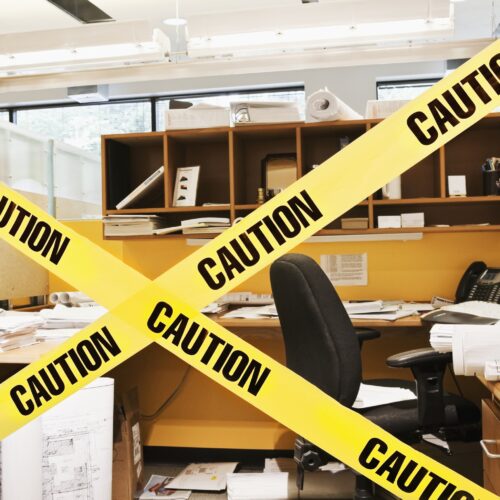
The First 48 When Ransomware Strikes
The content of this blog post comes from our webinar that you can watch here.[...]
Cyber Insurance. And The War on Ransomware.
The content of this blog post is based on our recent webinar that you can[...]
How Co-Managed IT Services Improve Your Patients’ Experience
Maximizing patient experience is one of the top priorities of healthcare businesses. In fact, it’s[...]
Business VPN: What are your options?
How and why businesses use VPN is a fascinating topic. If you know what VPN[...]
Business continuity: a crash course
We usually aren’t given much notice before a disaster strikes. Even with a little forewarning,[...]
Managed cybersecurity: The only way to stay ahead of the threat landscape
Cybersecurity is a concern for any modern business, no matter the size of the organization.[...]
Service Update
Recently, ISG Technology became aware of an IT security incident involving unauthorized access to our[...]
What’s the Difference between Co-Managed and Managed IT?
When it comes to managed IT services, there are two main options: co-managed and managed.[...]
The Benefits of Co-Managed IT Service for Healthcare Providers
Fast network speeds and a quality cybersecurity plan are probably not the first things that[...]
How to Become HIPAA Compliant
How to Become HIPAA Compliant HIPAA compliance is of utmost importance for any business that[...]